How to establish a route based VPN connection to AWS Hardware VPN
Hello Guys,
This post is the continuation of our conversation of establishing connection to AWS Hardware VPN. I am certainly not qualified to explain the differences between route based and policy based but I am hoping with these 2 posts it can be clear to you 😀 .For this experiment we are going to create a AWS Managed VPN in the California Region us-west-1 and get our VyOS EC2 instance from the Ohio region us-east-2 to connect to it.
10.0.0.0/16 # AWS VPN network.
172.20.0.0/16 # VyOS network
Here will be our plan of actions
- Create AWS VPN in Ohio
- Configure the VyOS with dynamic
Creating AWS Hardware VPN
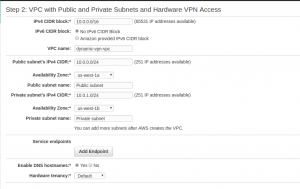
I have actually used the vpc wizard to set up this. I used the third option which sets up a public , a private subnet with a hardware VPN. I choose this wizard because it’s more like has all we wanted to do. I have not used the same VyOS as I used in the first part of this tutorials but there isn’t any reason you should not use the same.


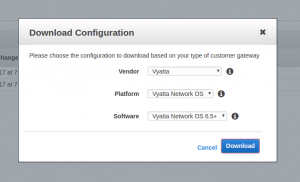
Generated AWS VPN Configuration
Below is the configuration that we generated for Vyatta. Vyatta is the ancestor from where VyOS is forked from.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 |
# ! Amazon Web Services ! Virtual Private Cloud ! AWS utilizes unique identifiers to manipulate the configuration of ! a VPN Connection. Each VPN Connection is assigned an identifier and is ! associated with two other identifiers, namely the ! Customer Gateway Identifier and Virtual Private Gateway Identifier. ! ! Your VPN Connection ID : vpn-287ae370 ! Your Virtual Private Gateway ID : vgw-4bda840e ! Your Customer Gateway ID : cgw-c182db84 ! ! ! This configuration consists of two tunnels. Both tunnels must be ! configured on your Customer Gateway. ! ! -------------------------------------------------------------------------------- ! IPSec Tunnel #1 ! -------------------------------------------------------------------------------- ! #1: Internet Key Exchange (IKE) Configuration ! ! A policy is established for the supported ISAKMP encryption, ! authentication, Diffie-Hellman, lifetime, and key parameters. ! Please note, these sample configurations are for the minimum requirement of AES128, SHA1, and DH Group 2. ! You will need to modify these sample configuration files to take advantage of AES256, SHA256, or other DH groups like 2, 14-18, 22, 23, and 24. ! The address of the external interface for your customer gateway must be a static address. ! Your customer gateway may reside behind a device performing network address translation (NAT). ! To ensure that NAT traversal (NAT-T) can function, you must adjust your firewall !rules to unblock UDP port 4500. If not behind NAT, we recommend disabling NAT-T. ! set vpn ipsec ike-group AWS lifetime '28800' set vpn ipsec ike-group AWS proposal 1 dh-group '2' set vpn ipsec ike-group AWS proposal 1 encryption 'aes128' set vpn ipsec ike-group AWS proposal 1 hash 'sha1' set vpn ipsec site-to-site peer 52.8.93.171 authentication mode 'pre-shared-secret' set vpn ipsec site-to-site peer 52.8.93.171 authentication pre-shared-secret 'rxKRlNfpmZ7z40djqmIAZShurR4MCB02' set vpn ipsec site-to-site peer 52.8.93.171 description 'VPC tunnel 1' set vpn ipsec site-to-site peer 52.8.93.171 ike-group 'AWS' set vpn ipsec site-to-site peer 52.8.93.171 local-address '18.220.200.250' set vpn ipsec site-to-site peer 52.8.93.171 vti bind 'vti0' set vpn ipsec site-to-site peer 52.8.93.171 vti esp-group 'AWS' ! #2: IPSec Configuration ! ! The IPSec (Phase 2) proposal defines the protocol, authentication, ! encryption, and lifetime parameters for our IPSec security association. ! Please note, you may use these additionally supported IPSec parameters for encryption like AES256 and other DH groups like 2, 5, 14-18, 22, 23, and 24. ! set vpn ipsec ipsec-interfaces interface 'eth0' set vpn ipsec esp-group AWS compression 'disable' set vpn ipsec esp-group AWS lifetime '3600' set vpn ipsec esp-group AWS mode 'tunnel' set vpn ipsec esp-group AWS pfs 'enable' set vpn ipsec esp-group AWS proposal 1 encryption 'aes128' set vpn ipsec esp-group AWS proposal 1 hash 'sha1' ! This option enables IPSec Dead Peer Detection, which causes periodic ! messages to be sent to ensure a Security Association remains operational. ! set vpn ipsec ike-group AWS dead-peer-detection action 'restart' set vpn ipsec ike-group AWS dead-peer-detection interval '15' set vpn ipsec ike-group AWS dead-peer-detection timeout '30' ! -------------------------------------------------------------------------------- ! #3: Tunnel Interface Configuration ! ! The tunnel interface is configured with the internal IP address. set interfaces vti vti0 address '169.254.8.202/30' set interfaces vti vti0 description 'VPC tunnel 1' set interfaces vti vti0 mtu '1436' ! -------------------------------------------------------------------------------- ! #4: Border Gateway Protocol (BGP) Configuration ! ! BGP is used within the tunnel to exchange prefixes between the ! Virtual Private Gateway and your Customer Gateway. The Virtual Private Gateway ! will announce the prefix corresponding to your VPC. ! ! Your Customer Gateway may announce a default route (0.0.0.0/0), ! which can be done with the 'network' statement. ! ! The BGP timers are adjusted to provide more rapid detection of outages. ! ! The local BGP Autonomous System Number (ASN) (65000) is configured ! as part of your Customer Gateway. If the ASN must be changed, the ! Customer Gateway and VPN Connection will need to be recreated with AWS. ! set protocols bgp 65000 neighbor 169.254.8.201 remote-as '7224' set protocols bgp 65000 neighbor 169.254.8.201 soft-reconfiguration 'inbound' set protocols bgp 65000 neighbor 169.254.8.201 timers holdtime '30' set protocols bgp 65000 neighbor 169.254.8.201 timers keepalive '10' ! To advertise additional prefixes to Amazon VPC, replace the 0.0.0.0/0 from the ! the following line with the prefix you wish to advertise. Make sure the prefix is present ! in the routing table of the device with a valid next-hop. set protocols bgp 65000 network 0.0.0.0/0 ! -------------------------------------------------------------------------------- ! IPSec Tunnel #2 ! -------------------------------------------------------------------------------- ! #1: Internet Key Exchange (IKE) Configuration ! ! A policy is established for the supported ISAKMP encryption, ! authentication, Diffie-Hellman, lifetime, and key parameters. ! Please note, these sample configurations are for the minimum requirement of AES128, SHA1, and DH Group 2. ! You will need to modify these sample configuration files to take advantage of AES256, SHA256, or other DH groups like 2, 14-18, 22, 23, and 24. ! The address of the external interface for your customer gateway must be a static address. ! Your customer gateway may reside behind a device performing network address translation (NAT). ! To ensure that NAT traversal (NAT-T) can function, you must adjust your firewall !rules to unblock UDP port 4500. If not behind NAT, we recommend disabling NAT-T. ! set vpn ipsec ike-group AWS lifetime '28800' set vpn ipsec ike-group AWS proposal 1 dh-group '2' set vpn ipsec ike-group AWS proposal 1 encryption 'aes128' set vpn ipsec ike-group AWS proposal 1 hash 'sha1' set vpn ipsec site-to-site peer 52.9.10.5 authentication mode 'pre-shared-secret' set vpn ipsec site-to-site peer 52.9.10.5 authentication pre-shared-secret 'p9f_CiwqQDnst4nhffaqFSyMD4RnNe7p' set vpn ipsec site-to-site peer 52.9.10.5 description 'VPC tunnel 2' set vpn ipsec site-to-site peer 52.9.10.5 ike-group 'AWS' set vpn ipsec site-to-site peer 52.9.10.5 local-address '18.220.200.250' set vpn ipsec site-to-site peer 52.9.10.5 vti bind 'vti1' set vpn ipsec site-to-site peer 52.9.10.5 vti esp-group 'AWS' ! #2: IPSec Configuration ! ! The IPSec (Phase 2) proposal defines the protocol, authentication, ! encryption, and lifetime parameters for our IPSec security association. ! Please note, you may use these additionally supported IPSec parameters for encryption like AES256 and other DH groups like 2, 5, 14-18, 22, 23, and 24. ! set vpn ipsec ipsec-interfaces interface 'eth0' set vpn ipsec esp-group AWS compression 'disable' set vpn ipsec esp-group AWS lifetime '3600' set vpn ipsec esp-group AWS mode 'tunnel' set vpn ipsec esp-group AWS pfs 'enable' set vpn ipsec esp-group AWS proposal 1 encryption 'aes128' set vpn ipsec esp-group AWS proposal 1 hash 'sha1' ! This option enables IPSec Dead Peer Detection, which causes periodic ! messages to be sent to ensure a Security Association remains operational. ! set vpn ipsec ike-group AWS dead-peer-detection action 'restart' set vpn ipsec ike-group AWS dead-peer-detection interval '15' set vpn ipsec ike-group AWS dead-peer-detection timeout '30' ! -------------------------------------------------------------------------------- ! #3: Tunnel Interface Configuration ! ! The tunnel interface is configured with the internal IP address. set interfaces vti vti1 address '169.254.10.90/30' set interfaces vti vti1 description 'VPC tunnel 2' set interfaces vti vti1 mtu '1436' ! -------------------------------------------------------------------------------- ! #4: Border Gateway Protocol (BGP) Configuration ! ! BGP is used within the tunnel to exchange prefixes between the ! Virtual Private Gateway and your Customer Gateway. The Virtual Private Gateway ! will announce the prefix corresponding to your VPC. ! ! Your Customer Gateway may announce a default route (0.0.0.0/0), ! which can be done with the 'network' statement. ! ! The BGP timers are adjusted to provide more rapid detection of outages. ! ! The local BGP Autonomous System Number (ASN) (65000) is configured ! as part of your Customer Gateway. If the ASN must be changed, the ! Customer Gateway and VPN Connection will need to be recreated with AWS. ! set protocols bgp 65000 neighbor 169.254.10.89 remote-as '7224' set protocols bgp 65000 neighbor 169.254.10.89 soft-reconfiguration 'inbound' set protocols bgp 65000 neighbor 169.254.10.89 timers holdtime '30' set protocols bgp 65000 neighbor 169.254.10.89 timers keepalive '10' ! To advertise additional prefixes to Amazon VPC, replace the 0.0.0.0/0 from the ! the following line with the prefix you wish to advertise. Make sure the prefix is present ! in the routing table of the device with a valid next-hop. set protocols bgp 65000 network 0.0.0.0/0 ! Additional Notes and Questions ! - Amazon Virtual Private Cloud Getting Started Guide: ! http://docs.amazonwebservices.com/AmazonVPC/latest/GettingStartedGuide ! - Amazon Virtual Private Cloud Network Administrator Guide: ! http://docs.amazonwebservices.com/AmazonVPC/latest/NetworkAdminGuide ! - XSL Version: 2009-07-15-1119716 |
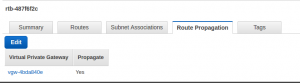
Enabling Route propagation on AWS VPN network
Here is the tricky part that got me when I did this. On previous tutorial, I manually created the routes on the VPC route table to point to AWS Vitual Gateway then any box on the VPC want to connect to the VyOS side. I reckon in the previous post as well, Route propagation can be done for the listed encryption domain in there. Here in our case there is no encryption domain to create route for. So Having the BGP to advertise the VyOS network to AWS VPN network, finally gets to the AWS VPN route table when Route propagation is enabled. You can find this under route table page of the actual vpc.

Creating Firewall Rules
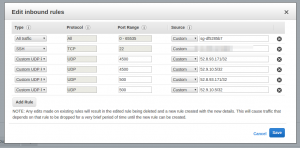
Rules on AWS VPN side
For a complete simulation , I have created a small t2.nano EC2 to serve as node behind the AWS VPN. Below is the security group for inbound connection from VyOS side
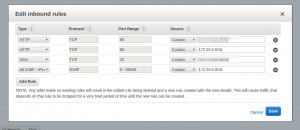
As you can see we have opened port 80 and all ports on ICMP for all traffic coming from VyOS nework
Rules on the VyOS side
Rule on VyOS itself
There is here as well a box to serve as node behind VyOS. VyOS itself being a node has its separate firewall rules.
Rules on box behind VyOS
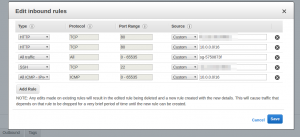
We need to manually create a entry in route table on VyOS side to send to VyOS all traffic going towards 10.0.0.0/16 network
Configuring VPN on VyOS
As indicated already , I have used a different VyOS for this setup but you can use the same box as used in the first part of this series. I have for this reason used vti 2 and 3 instead as in continuation of the configuration done on the first part. In configuration mode, please enter the following commands.
Creating Virtual Interfaces
|
1 2 3 4 5 6 7 8 |
# set interfaces vti vti2 description "VyOSEAST_AWSWEST_VPN tunnel 1" set interfaces vti vti2 address 169.254.8.202/30 set interfaces vti vti2 mtu 1436 set interfaces vti vti3 description "VyOSEAST_AWSWEST_VPN tunnel 2" set interfaces vti vti3 address 169.254.10.90/30 set interfaces vti vti3 mtu 1436 |
Creating IKE and ESP Settings
We are using the same group as in first part. If you are using the same box , you can skip this part.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
# set vpn ipsec ike-group IKE-AES256-SHA1-LT28800 lifetime 28800 set vpn ipsec ike-group IKE-AES256-SHA1-LT28800 proposal 1 dh-group 2 set vpn ipsec ike-group IKE-AES256-SHA1-LT28800 proposal 1 encryption aes256 set vpn ipsec ike-group IKE-AES256-SHA1-LT28800 proposal 1 hash sha1 set vpn ipsec ike-group IKE-AES256-SHA1-LT28800 dead-peer-detection action restart set vpn ipsec ike-group IKE-AES256-SHA1-LT28800 dead-peer-detection interval 15 set vpn ipsec ike-group IKE-AES256-SHA1-LT28800 dead-peer-detection timeout 30 set vpn ipsec esp-group ESP-AES256-SHA1-LT3600 lifetime 3600 set vpn ipsec esp-group ESP-AES256-SHA1-LT3600 mode tunnel set vpn ipsec esp-group ESP-AES256-SHA1-LT3600 pfs enable set vpn ipsec esp-group ESP-AES256-SHA1-LT3600 proposal 1 encryption aes256 set vpn ipsec esp-group ESP-AES256-SHA1-LT3600 proposal 1 hash sha1 |
Creating IPSEC Configuration
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 |
# set vpn ipsec ipsec-interfaces interface eth0 set vpn ipsec nat-traversal enable edit vpn ipsec site-to-site peer 52.8.93.171 set description "VyOS US EAST 1A Region to AWS Hardware VPN US WEST 1 tunnel 1" set authentication mode pre-shared-secret set authentication pre-shared-secret 'rxKRlNfpmZ7z40djqmIAZShurR4MCB02' set connection-type initiate set ike-group IKE-AES256-SHA1-LT28800 set local-address 172.20.0.31 set vti bind vti2 set vti esp-group ESP-AES256-SHA1-LT3600 top edit vpn ipsec site-to-site peer 52.9.10.5 set description "VyOS US EAST 1A Region to AWS Hardware VPN US WEST 1 tunnel 2" set authentication mode pre-shared-secret set authentication pre-shared-secret 'p9f_CiwqQDnst4nhffaqFSyMD4RnNe7p' set connection-type initiate set ike-group IKE-AES256-SHA1-LT28800 set local-address 172.20.0.31 set vti bind vti3 set vti esp-group ESP-AES256-SHA1-LT3600 top |
Configuring dynamic routes
|
1 2 3 4 5 6 7 8 9 10 |
# set protocols bgp 65000 neighbor 169.254.8.201 remote-as '7224' set protocols bgp 65000 neighbor 169.254.8.201 soft-reconfiguration 'inbound' set protocols bgp 65000 neighbor 169.254.8.201 timers holdtime '30' set protocols bgp 65000 neighbor 169.254.8.201 timers keepalive '10' set protocols bgp 65000 neighbor 169.254.10.89 remote-as '7224' set protocols bgp 65000 neighbor 169.254.10.89 soft-reconfiguration 'inbound' set protocols bgp 65000 neighbor 169.254.10.89 timers holdtime '30' set protocols bgp 65000 neighbor 169.254.10.89 timers keepalive '10' |
Creating static routes
I think at this point the astute reading would probably raise his/her eyebrows. The reason why anything here is static is because, in order to get VyOS advertise the network at VyOS side, VyOS itself needs to have that route in its local route table. We are just adding that. it’s more like stating the obvious but it’s pretty essential for the AWS VPN side to receive VyOS network route. This is the only simpler explanation I could come up with for now.
|
1 2 3 |
# set protocols static route 172.20.0.0/16 next-hop 172.20.0.1 distance 10 set protocols bgp 65000 network 172.20.0.0/16 |
Persist Configuration
|
1 2 3 |
# commit save |
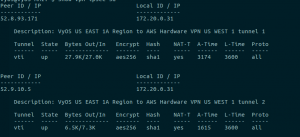
Verification

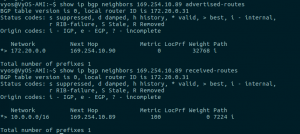
On the image above we could see AWS VPN is up and has Route advertised from VyOS box. On the image below, we have status being up for VyOS as well
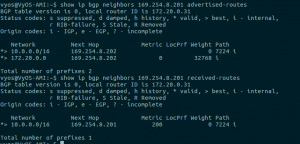
Showing route advertised to and received from AWS VPN
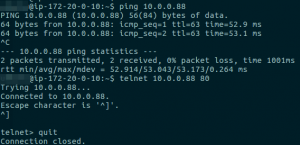
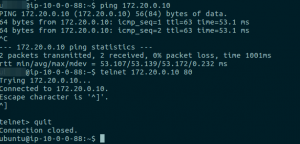
Testing connectivity
That’s it, I hope this has been useful to you.
Thanks for reading.